Rings of Protection: Reducing Your Vulnerability to a Terrorist Attack
Any asset can be a target for terrorists. How well we protect our assets is up to us.
- By Brian Bennett
- Jun 01, 2004
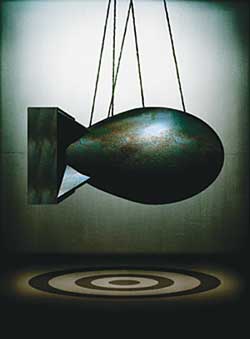 THE terrorist threat is all too real. Terrorists can choose from
a wide variety of attacks to execute against this country, including
kidnapping, murder, cyber, product adulteration, or use of weapons of
mass destruction (biological, nuclear, incendiary, chemical, or
explosive agents).
THE terrorist threat is all too real. Terrorists can choose from
a wide variety of attacks to execute against this country, including
kidnapping, murder, cyber, product adulteration, or use of weapons of
mass destruction (biological, nuclear, incendiary, chemical, or
explosive agents).
Every business has assets, whether they are people, information, equipment, services, or products. Every asset is vulnerable to attack, and every asset can be protected. How much we spend to protect that asset (e.g., cost, practicality, and reasonability) is up to us.
Terrorists (the bad guys) could target an asset for a number of reasons--it is a piece of critical infrastructure; destruction of the asset will have a significant negative financial impact on a company, a region, the country, or the world; attacking the critical asset is a diversion for another attack elsewhere; or the asset itself can be used as a weapon of mass destruction. The bad guys are not going to expend resources on attacks that are not likely to succeed. The simple reason for this is that terrorism costs money. The bad guys need to invest substantial amounts of time, energy, and money to put an attack together.
The Terrorist's Investment
In order to plan and execute an attack, the terrorist leadership must invest in their cause. The terrorists must sell their plan to both their leadership and supporters in order to secure the resources they need. Their three major investment categories are:
- Time: The bad guys must recruit the operative(s) to plan and conduct the attack. This person(s) must be smart, reliable, motivated, and trainable. The training period can be extensive, with significant amounts of time spent not only on executing the attack, but also in preparation (recruiting, planning, reconnaissance, logistics, and transportation). Depending on the complexity of the attack, the training period can take weeks, months, or even years.
- Equipment: The bad guys will need a laundry list of equipment in order to succeed, everything from transportation to housing, to the weapons needed for the attack. Some of the equipment is legal, cheap, and easy to obtain (computers), while other equipment is illegal, more expensive, and takes longer to develop the right relationships in order to obtain (weapons of mass destruction).
- Money: Significant financial resources may be needed to develop and execute an attack. Money will be needed to feed, transport, and house the terrorists (and maybe their families); to provide the training necessary to plan and execute the attack; and to purchase the resources needed to successfully plan, reconnoiter, and execute the attack.
The bad guys want to protect their investment. They want the operative to be able to execute the attack and be available for another attack on another day. A successful attack will result in the terrorists' reaping increased morale, better propaganda, and additional financial donations to their cause, and it will greatly aid in their recruiting efforts. Therefore, they will not go against our strength or even our perceived strength. In the terrorist's world, perception is reality.
What Can We Do?
In order to protect our people and facilities, we need to convince the bad guys they do not want to risk expending the resources on an attack that is not likely to succeed. We need to implement rings of protection for our critical assets, whether they are people, infrastructure, economic, equipment, products, or intellectual.
The basic criteria for vulnerability to attack are intent, motivation, capability, and ease of attack. If any one element is removed, the chain is broken and vulnerability approaches zero. Clearly, the only leg over which we have direct influence is ease of attack. Remember that the bad guys need the attack to be successful, and they will not go against our strength or even our perceived strength. We must convince the terrorists an attack against our facility would not succeed and therefore would be a poor investment of their resources.
Rings of Protection: Three Ds and an R
A well-structured protection plan will have four overlapping and intermixed rings of protection: deter, detect, delay, and respond. Rings of protection that are properly deployed will not only provide real security, but also a perception of security that goes beyond the actual improvements installed.
The chances for success of dissuading an attack increase greatly and become value added when the rings of protection overlap, and one enhancement will provide value in multiple rings (i.e., a properly trained and equipped security guard can deter, detect, delay, and respond).
- Deter--Remember, perception is reality to the bad guys. Every asset is a potential target, so there are plenty of choices to select from and plenty of opportunity to attempt an attack. The best indicator that an asset may be targeted is direct observation or evidence that an asset is or has been under surveillance. Therefore, the goal at this outermost ring of protection is to "scare the bad guys away." You need to convince them the chance of successfully executing an attack against this asset is low and not worth expending their resources on. We know the bad guys will reconnoiter a target before executing an attack, so if we can scare them away quickly we can interrupt the planning process and avoid being targeted.
Examples of deterrents include highly visible and professional-appearing security forces that make frequent, random patrols, as well as man fixed security points; appropriate levels of fencing, lighting, access control, and intrusion detection; and provisions for personal and vehicle inspections, as well as identification and background checks of individuals as one gets closer to the critical asset.
- Detect--The earlier the planning, reconnaissance, or attack itself is detected and interrupted, the less likely it is to succeed. Optimally, the attack should be detected during the planning or reconnaissance stage by having systems in place to reveal the presence of the bad guy trying to collect intelligence about the critical asset. Training employees about specific activities that should be considered suspicious and how to report this to the appropriate authority would be the outermost level of detection. Background checks and searches are valuable in screening potential employees, contractors, truck drivers, and visitors before they enter the facility. Intrusion detection systems, surveillance cameras, alarms, and frequent, random inspection rounds by security guards make up the innermost level of the detect ring.
- Delay--If we are unable to deter or detect the bad guy, we must have sufficient physical and administrative barriers in place to make it difficult to gain clear and direct access to the critical asset. We must take the appropriate steps to ensure the bad guys do not have a straight run directly to the target. Typical delaying tactics include remote check-in points; verification of identity and purpose of visits; searching of person, parcels, and vehicles; multiple layers of fencing or other physical blocking devices such as tire shredders and "jersey barriers"; and locked doors with access control systems.
- Respond--If all else fails, we must have the appropriate capability to respond to the likely consequences of a successful attack. Emergency pre-planning activities must change their focus from the traditional "accidental" damage scenario to the current "on purpose" scenario, whereby someone is intentionally trying to cause the greatest amount of damage and casualties. Local law enforcement agencies must now participate in the pre-emergency planning process to include security issues. Careful review and coordination of both the municipal and private industry joint response capabilities and equipment must be completed, with clearly delineated areas of responsibility. There must be redundant capabilities for communications and mitigation. Pre-emergency planning and periodic emergency exercises with fire, emergency medical services, and law enforcement increase the chances of success. A strong emergency response capability also can serve as a deterrent to an attack if the bad guys believe the consequences will be quickly and successfully mitigated.
Conclusion
Every asset is a potential target, and every asset can be protected. The bad guys need their attack to be successful and therefore will not go against our perceived strength. Our job is to establish overlapping and intermixed rings that will provide perceived and actual protection against attack.
The only real defense we have in preventing an attack against our asset is to eliminate the terrorist's perception that an attack can be easily executed. We must revisit our hazard assessments and emergency pre-plans with an eye toward the intentional act and the more severe consequences a successful attack will bring.
We must work closely not only with the fire and the emergency medical service, but with law enforcement as well in the planning and execution of emergency exercises. We must partner with the local municipal emergency responders to pool our personnel and equipment to ensure the quickest, most efficient, and safest response in the event of an attack.
This article originally appeared in the June 2004 issue of Occupational Health & Safety.